In its classic version, PILAR associates ICT threats with system assets, threats that affect ICT dimensions (confidentiality, integrity, etc.) and calculates the mitigating effect of ICT security measures to estimate residual risk.
The same approach:
![]()
can be applied in
wider scenarios. In what follows we will apply it to the legal aspects (legal
risk) of the assets that have value because of their personal character.
The approach is to
associate threats on the legal aspects of the processing of personal data and
apply measures that address such threats.
The value is
determined by the valuation of the asset in the privacy dimension. The threat
must be identified together with its impact on the value of the asset and the
estimated probability of occurrence (ARO). The measures that are adopted reduce
the risk. All this within the unified framework for estimating potential and
residual risks.
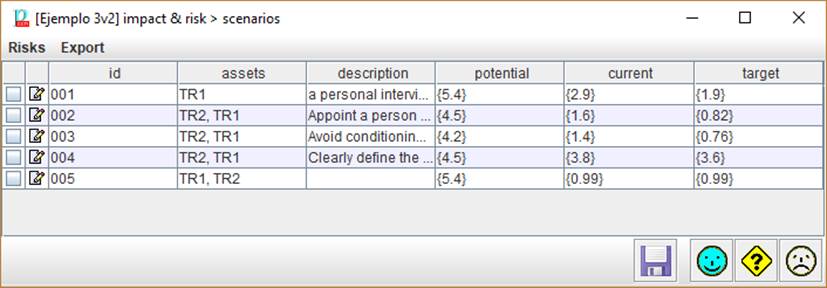
Top toolbar
|
Risk |
new to create a new row edit to modify a row delete to delete a row |
|
Export |
CSV table to CSV for Excel XML table to XML |
Bottom toolbar
|
|
Saves current project
either in a file, or in database (according to its source). |
|
|
OK. The changes are saved, and the screen is closed. |
|
|
CANCEL. The changes are undone, and the screen is closed. |
|
|
HELP. Jumps into this help files. |
Table
|
|
Allows you to
select some rows; click to select or forget; with the shift key you can
select a range |
|
|
Click to edit
the row |
|
id |
Row identifier:
it should be a unique identifier, without duplicates |
|
assets |
One or more
assets involved in the described scenario. |
|
description |
A textual
description. It shall describe both the threat scenario and the measures to
counter it. |
|
phases |
As many columns
as projects phases, starting with the potential phase (inherent risk). It
shows the residual risk in each phase. |
You may SHIFT-UP to
move one or more selected scenarios one step upwards.
You may SHIFT-DOWN to
move one or more selected scenarios one step downwards.