Currently only for logical borders.
This screen presents the paths that attackers may follow from external origin to target zones. For each threat and phase, PILAR presents the estimated likelihood (of success) and risk.
For likelihood, the screen looks like this
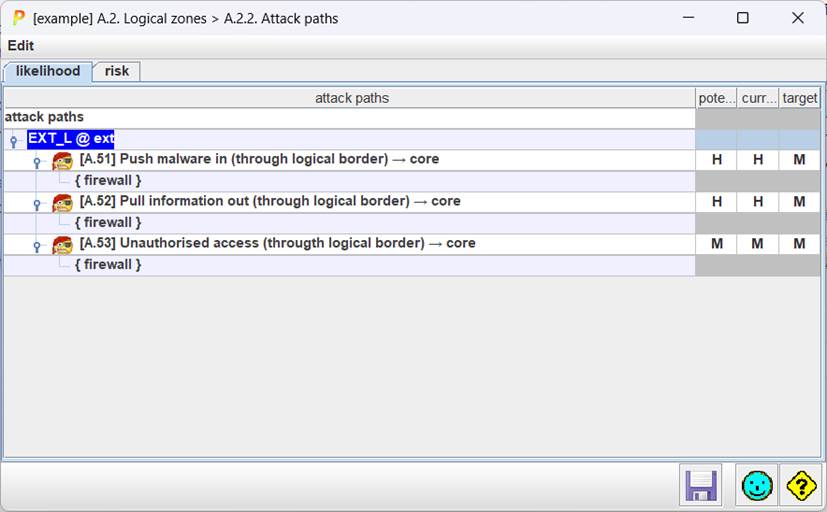
Let’s read it.
Row 1
For external attackers EXT_L at ext zone.
Row 2 (and 4, and 6)
Exercising threat A.51, the attacker may push malware thru border device “firewall” (row 3) into internal zone “core”.
The columns present likelihood of the attack for each phase.
For risk, the screen looks like this
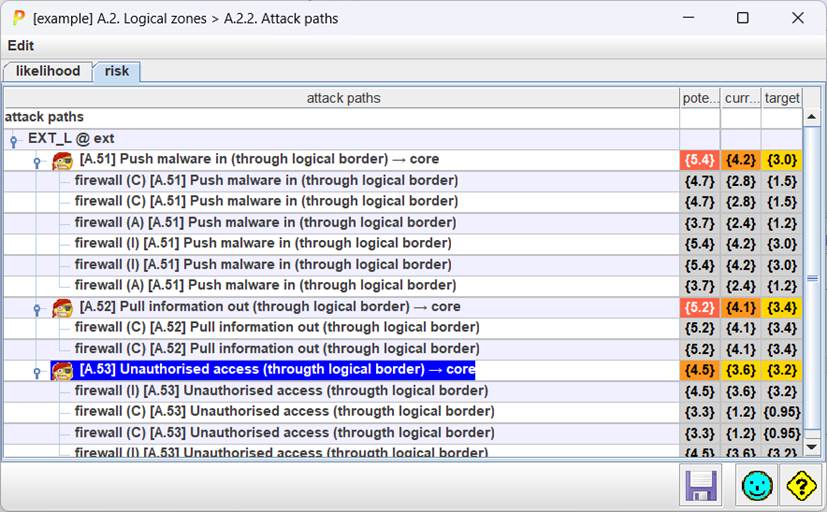
It is quite similar as for likelihood, but impact may affect more than one dimension, and PILAR presents one row for each.