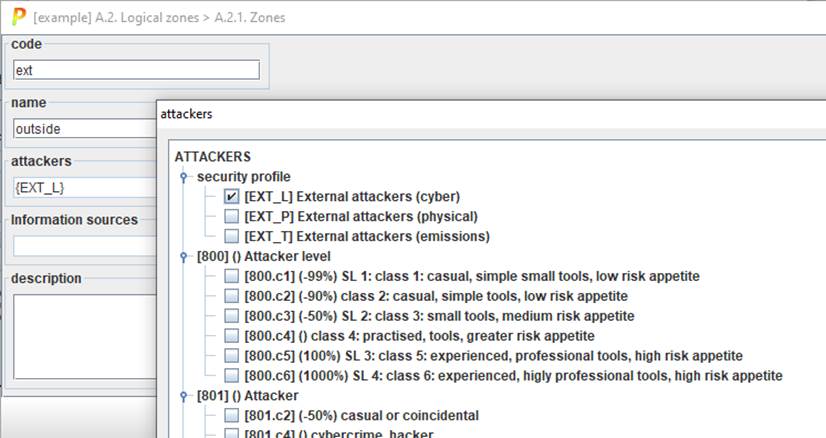
While creating a new zone, or editing it afterwards, users may determine its (unique) code, a descriptive name, information sources, and a verbose description (that may link to an internal web repository.
Most relevant, users may specify the attacker profile, for attacks starting from this zone.
Attack profiles are described by means of TSV specification files, referred from the configuration (CAR) file:
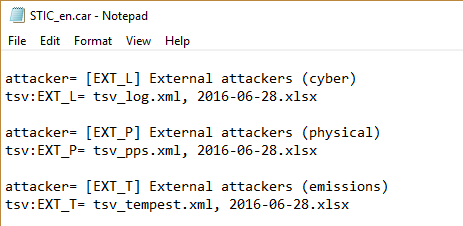
For a logical attacker like EXT_L, his capabilities on border system are described in tsv_log.xml. Once the border is passed, its capabilities are described by means of 2016-06-28.xlsx.