Security profiles are collections of safeguards that aim to protect a system. Security profiles may focus on some specific aspects or may be general. There are security profiles that are widely recognized and can be checked for compliance.
PILAR maps security profiles to her safeguards in such a way that:
· you may estimate to which extend the system is compliant
· PILAR may estimate the residual risk after satisfying the profile
· you may work with several profiles in a coordinated manner
Let’s use ISO/IEC 27002 (2013) as an example.
To load it into PILAR, you need the corresponding .EVL file
bib_en/27002_2013_*_en.evl
and you have to configure PILAR to load it on start (alternatively, you may load later, through the user interface). From the configuration file:
STIC_en.car
profile= 27002_2013_ * _en.evl
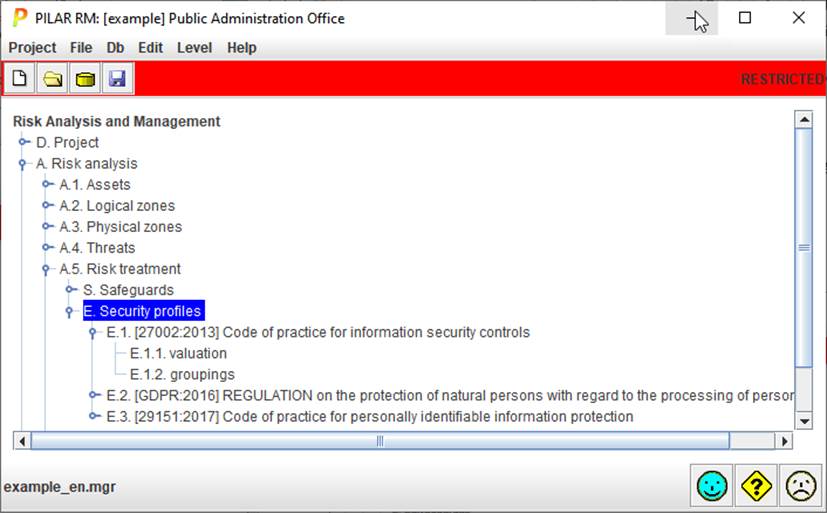
In the GUI, the loaded profiles appear as:
And, getting into valuation, we
find the collection of controls of the standard:
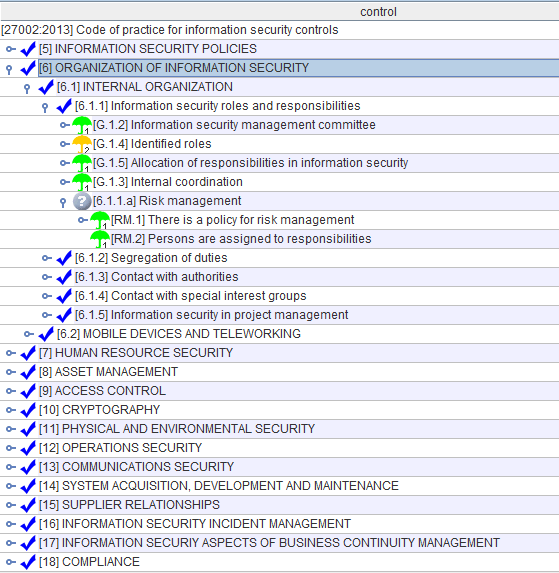
EVL trees have different types of nodes:
|
|
Controls – main requirements from security profiles |
|
|
Questions – secondary requirements, or tree structuring nodes |
|
|
Links – when a control refers to another control |
|
|
Safeguards – countermeasures from the PILAR library |
|
|
See also – additional information |