Top menu EDIT
|
find |
search text in tree |
|
question |
jumps to next question in tree |
|
options |
See Edit_options |
Top menu EXPAND
|
controls |
Expands tree to show controls |
|
questions |
Expands tree to show questions |
|
safeguards |
Expands tree to show safeguards |
|
dual
role |
Selects those safeguards that contribute to two or more controls |
|
n.a. |
Expands tree to show not applicable controls |
|
{xor} |
Expands tree to show alternative options, to select |
|
perimeter |
See Perimeters |
Top menu VIEW
|
maturity |
Show maturity levels; either simple values, or a rank when children are of different maturity. |
|
~maturity |
Show maturity levels; when children have different maturities, an average is shown. |
|
percent |
A percent, between 0% and 100%, taking safeguards as source. |
|
PILAR |
A percent, relative to column PILAR. |
|
one
line |
For tree entries that require more than one line, show only first line. |
|
one
paragraph |
For tree entries that require more than one line, show full text |
Top menu EXPORT
|
CSV |
The visible rows are copied to a CSV file |
|
XML |
The values are copied to an XML file |
|
database |
The values are copied to an external database (if license allows database access) |
|
SoA |
A report is generated with the controls
that apply |
|
report |
The values are copied to a textual file (RTF or HTML) |
|
report
(< Lx) |
A report is generated with the safeguards below a given threshold |
|
report
(< target) |
A report is generated with the safeguards below target phase.See “Safeguards / Reference and target phases” below. |
|
report
(suggest) |
Generates a report with suggested improvements. It compares selected phase with extra phase and prints both maturity values. Results are grouped by controls, and sorted. |
Top menu IMPORT
|
from
CSV |
Read maturity values from a CSV file |
|
from
XML |
Read maturity values from an XML file |
|
from
EVL |
from other profile (evl) |
|
import
(mgr) |
|
|
import
(db) |
|
To import from another project, PILAR presents a list of possible sources and destinations. Sources are security profiles in the project to import. Destinations are security profiles in this project. Sources and destinations are linked by profile code, and by association files.
Top menu SELECT
|
clear |
clear selection |
|
level
1 |
select controls on tree level 1 |
|
level
2 |
select controls on tree level 2 |
|
level
3 |
select controls on tree level 3 |
|
current
situation |
select controls currently visible |
|
mandatory |
select controls that are mandatory |
|
project
phases |
select phases for graph |
Top menu GRAPHS
|
draw |
Drawing with the current selection of rows and phases. |
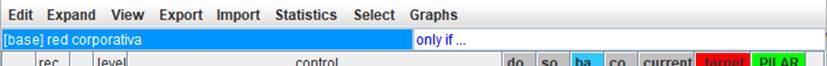
Top bands
|
security domain |
There may be different controls for different domains. Click to select the domain you want to edit. |
|
only if … |
Click to select some controls based on attributes. After that, PILAR will prune the tree to show only the parts of the tree related to the selected items. You may select different criteria to match · controls that apply or that do not apply · information sources · applicability level |
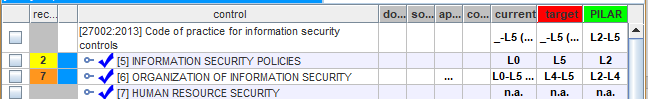
Table columns
|
1 |
select |
Selects rows for graphs. Click on checkboxes to check / uncheck. SHIFT-click to check a range. Click on column header to clear current selection. |
|
2 |
recommendation |
It is a rank in the range [null .. 10], estimated by PILAR taking into account the assets, the security dimensions, and the level of risk addressed by this safeguard. The cell is grey if PILAR finds no reason to recommend this row. That is, PILAR does not know which risk this row is good for. (o) - PILAR thinks it is an overkill (“too much”). (u) - PILAR thinks it is an under-kill (“not enough”). |
|
3 |
traffic light |
Compares valuation in reference phase (RED) with valuation in target phase (GREEN), and shows a colour: RED reference phase value is far below target phase value YELLOW reference phase value is close below target phase value GREEN reference phase value is equal to target phase value BLUE reference phase value is higher than target phase value See “EVL / Reference and target phases” below. |
|
4 |
controls |
Presents hierarchically the controls in the security profile, and the mapping onto safeguards. You double click to collapse / expand the tree. You may right-click to access to tree menu. |
|
5 |
doubts |
Click to mark / unmark the row. The mark is typically used to remember that there are issues waiting for an answer. The mark “floats” to the top level to highlight the problem. |
|
6 |
sources |
Click to associate information sources to the row and its children. |
|
7 |
applies |
|
|
8 |
comment |
Click to associate comments to the row. |
|
9 … |
|
Project phases. Left-click to select reference phase (RED). Right-click to select target phase (GREEN). · See “EVL / Reference and target phases” · See “EVL / Valuation |
Bottom toolbar
|
|
Spinner to control the expansion of the tree |
|
|
Modifies the behaviour of spinner. If selected, the expansion includes mapped safeguards. If unselected, expansion stops before presenting safeguards. |
|
domains |
See EVL / domain |
|
|
Undo last changes. |
|
|
Redo last undone changes. |
|
suggest |
Presents a sorted list of controls that deserve improvements. In order to sort, PILAR takes into account the relative importance if the control and the maturity gap between current phase and target phase. |
|
|
Saves current project either in a file, or in database (according to its source). |